Understanding Agentic Commerce Payments
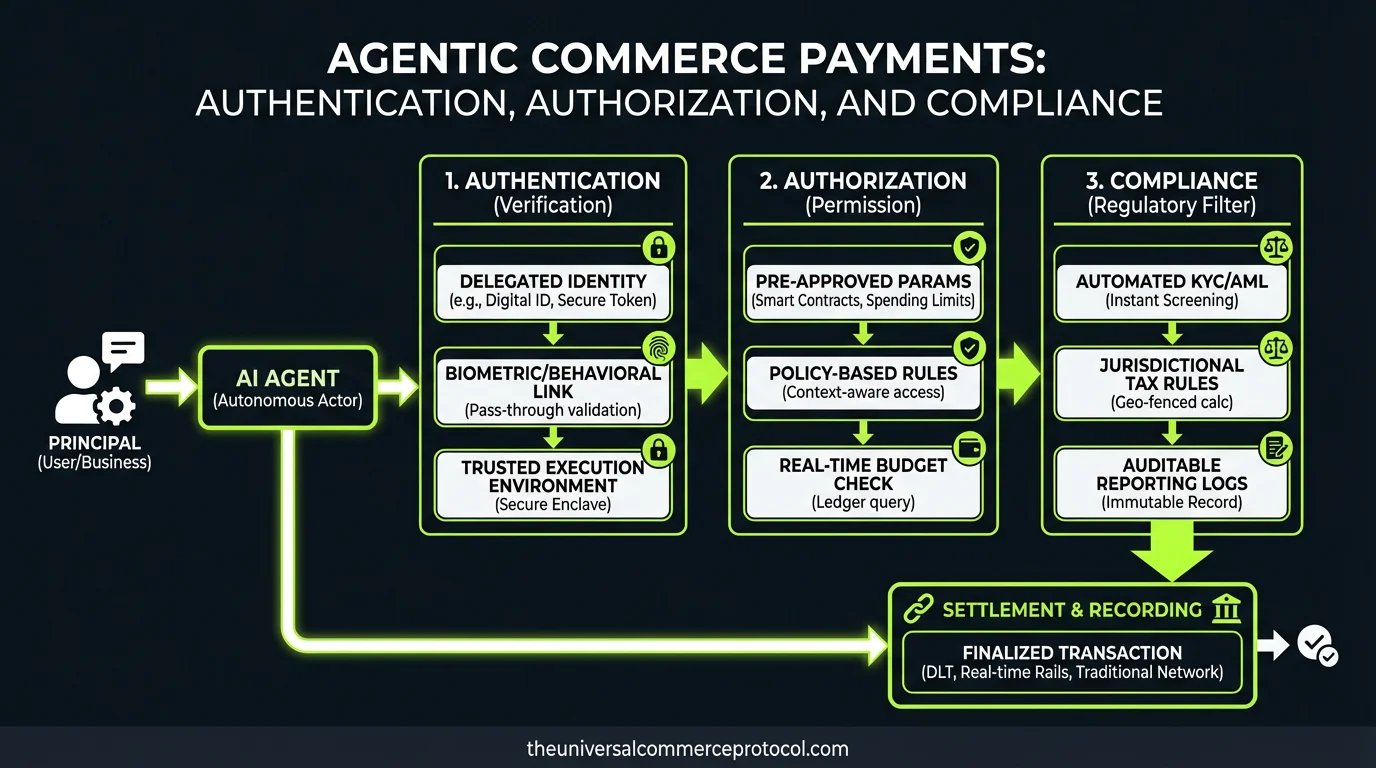
Agentic commerce payments represent a fundamental shift in how transactions occur within distributed commerce ecosystems. Unlike traditional e-commerce where human intervention initiates each purchase, agentic commerce enables autonomous agents to execute payment transactions on behalf of users, organizations, or other agents. These transactions occur within the Universal Commerce Protocol (UCP) framework, which standardizes how agents interact, negotiate, and settle payments across heterogeneous systems.
The complexity of agentic commerce payments stems from multiple simultaneous requirements: agents must authenticate their identity and authorization scope, comply with financial regulations across jurisdictions, protect sensitive payment data, and maintain audit trails for dispute resolution. Traditional payment processing was designed for synchronous human-initiated transactions; agentic payments demand asynchronous, permission-based, and verifiable execution models.
Authentication Frameworks for Autonomous Agents
Agent Identity and Cryptographic Verification
Authentication in agentic commerce payments begins with establishing verifiable agent identity. Unlike human users with username-password combinations, autonomous agents require cryptographic identity mechanisms that can be verified programmatically and scaled across thousands of concurrent transactions.
The Universal Commerce Protocol implements agent authentication through public-key cryptography, where each agent maintains a cryptographic keypair. When an agent initiates a payment transaction, it signs the transaction with its private key, allowing any participant in the commerce network to verify the agent’s identity using its public key. This approach eliminates the need for centralized identity providers and enables peer-to-peer verification.
Major payment infrastructure providers have begun supporting agent-based authentication models. Stripe, through its Connect platform, enables applications to act as agents on behalf of merchants, with OAuth 2.0 scopes defining what payment actions each agent can perform. Similarly, PayPal’s commerce platform supports delegated authentication where applications authenticate as agents within defined permission boundaries.
Multi-Signature Authorization
High-value agentic commerce payments often require multi-signature authorization, where transactions must be cryptographically signed by multiple parties before execution. This prevents rogue agents from executing unauthorized payments and provides additional security for critical transactions.
In the UCP framework, multi-signature schemes define which parties must authorize a transaction based on payment amount, agent reputation score, or transaction type. A procurement agent purchasing raw materials might require signatures from both the agent itself and a financial controller agent before funds transfer. Blockchain-based payment systems like those integrated with Ethereum or Hyperledger Fabric natively support multi-signature requirements, enabling complex authorization workflows.
Authorization and Permission Scoping
Granular Permission Models
Authorization determines what payment actions a specific agent can execute. Rather than granting blanket payment authority, agentic commerce implements granular permission scoping that restricts agents to specific transaction parameters.
The OAuth 2.0 framework, widely adopted in payment systems, provides a foundation for this scoping. An authorization scope might specify: a maximum transaction amount ($10,000), allowed payment methods (credit card, ACH, wire transfer), permitted merchant categories (suppliers only), and time windows (business hours only). Agents attempting transactions outside these scopes are rejected before payment processing begins.
Advanced permission models implement dynamic scoping based on real-time factors. A procurement agent’s authorization limit might increase based on its transaction history and success rate, or decrease if suspicious patterns emerge. This requires integration with fraud detection systems that monitor agent behavior continuously.
Delegation and Sub-Agent Authorization
Complex commerce ecosystems often involve agent hierarchies where primary agents delegate payment authority to sub-agents. A supply chain agent might delegate purchasing authority to category-specific agents (one for raw materials, another for packaging), each with distinct permission boundaries.
The UCP framework supports delegation chains with explicit authorization records. Each delegation event creates an immutable record specifying which permissions transferred from parent to child agent, with revocation capabilities at any level. This prevents unauthorized permission escalation and enables rapid response if a sub-agent is compromised.Payment processors like Amazon Pay for Business and SAP Concur have implemented delegation models where organizations define hierarchical approval workflows. These systems maintain complete audit trails showing which agent authorized each transaction and whether that authorization was delegated from a higher authority.
Compliance Requirements in Agentic Payments
Know Your Agent (KYA) Protocols
Traditional financial compliance relies on Know Your Customer (KYC) procedures where institutions verify human identity. Agentic commerce requires parallel Know Your Agent (KYA) frameworks that establish agent provenance, ownership, and intended use.
KYA protocols define requirements for agent registration, including: owner/operator identification, agent purpose and use case, transaction volume expectations, and integration with human oversight mechanisms. Financial institutions must verify that agents are operated by legitimate entities and not designed for fraud or money laundering.
The Financial Action Task Force (FATF) has begun addressing autonomous transaction systems in its guidance on virtual assets and money laundering. While specific agentic commerce guidance remains emerging, FATF principles require that institutions maintain visibility into who controls autonomous agents and can interrupt transactions when suspicious patterns emerge.
Transaction Monitoring and Suspicious Activity Detection
Agentic commerce payments execute at machine speed, making real-time transaction monitoring essential. Unlike human payment reviewers who can intervene after suspicious transactions, agentic systems must prevent unauthorized transactions before settlement.
Compliance systems integrate behavioral analysis, pattern recognition, and rule-based detection. Suspicious patterns include: transactions deviating significantly from agent historical behavior, payments to new or high-risk merchants, circular transaction patterns suggesting money laundering, or rapid sequential transactions suggesting account compromise.
Major payment networks have invested heavily in this capability. Mastercard’s Decision Intelligence and Visa’s Advanced Authorization platform use machine learning to evaluate transaction risk in real-time, with particular attention to novel transaction patterns from autonomous systems. These systems can flag agentic transactions for additional verification without blocking legitimate commerce.
Regulatory Reporting and Audit Requirements
Financial regulations across jurisdictions require detailed transaction reporting. In the United States, the Bank Secrecy Act mandates Suspicious Activity Reports (SARs) for transactions meeting certain criteria. The European Union’s Anti-Money Laundering Directive requires member states to maintain transaction records for five years and report suspicious activity to Financial Intelligence Units.
Agentic commerce systems must generate compliance-ready reports automatically. Every agent payment must be logged with: transaction amount, parties involved, timestamp, authorization details, and risk assessment results. The UCP framework standardizes these logging requirements, ensuring that agents operating across multiple payment networks generate consistent compliance records.
Blockchain-based payment systems offer inherent compliance advantages through immutable transaction records. Hyperledger Fabric deployments in financial consortiums maintain tamper-proof transaction histories that satisfy regulatory audit requirements automatically.
Data Security and PCI DSS Compliance
Payment Card Industry Standards
Any agentic commerce system handling credit card data must comply with Payment Card Industry Data Security Standard (PCI DSS). This requirement applies whether agents process cards directly or through payment processors.
PCI DSS mandates encryption of cardholder data in transit and at rest, network segmentation preventing unauthorized access, regular security assessments, and incident response procedures. For agentic systems, this means agents cannot store raw card data; they must tokenize payment information immediately and use tokens for subsequent transactions.
Tokenization providers like Stripe, Square, and Adyen manage this complexity. Agents receive tokens representing payment methods rather than card details, eliminating PCI compliance burden while enabling autonomous transactions. The UCP framework standardizes tokenization requirements, ensuring agents across different commerce networks work with consistent payment representations.
Encryption and Key Management
Agentic commerce payments require sophisticated encryption protecting data both in transit and at rest. Transport Layer Security (TLS) 1.3 provides encryption for data in transit, while Advanced Encryption Standard (AES-256) protects stored payment information.
Key management becomes critical at scale. Agents operating thousands of daily transactions need access to encryption keys without storing them locally (which creates security vulnerabilities). Hardware Security Modules (HSMs) and key management services like AWS Key Management Service provide centralized key storage with audit logging.
Dispute Resolution and Chargeback Management
Transaction Immutability and Audit Trails
When payment disputes arise, complete transaction records are essential. Agentic commerce systems must maintain immutable records showing: agent identity, authorization details, transaction parameters, compliance checks performed, and settlement confirmation.
The UCP framework requires that all agentic payment transactions generate cryptographic proofs of execution. These proofs demonstrate that a specific agent, with specific authorization, executed a transaction at a specific time. This evidence is invaluable when disputing chargebacks or resolving transaction disagreements.
Chargeback Prevention
Chargebacks represent significant costs for payment processors and merchants. Agentic commerce systems can reduce chargebacks through better transaction authentication and authorization, since agents provide verifiable proof of authorization that human cardholders cannot easily dispute.
However, new chargeback categories are emerging around agent-executed transactions. Payment networks are developing specific guidance for disputes involving autonomous agents, including scenarios where agents were compromised or operated outside their authorization scope.
Emerging Standards and Future Directions
ISO 20022 for Agent Payments
The International Organization for Standardization (ISO) is developing extensions to ISO 20022 (the financial messaging standard) to accommodate agentic transactions. These extensions standardize how agent identity, authorization, and compliance information flows through payment networks.
Decentralized Identity for Agents
Decentralized Identifiers (DIDs) and Verifiable Credentials are emerging technologies that could transform agent authentication. Rather than relying on centralized identity providers, agents could maintain self-sovereign identities with cryptographically verifiable credentials demonstrating their authorization scope and compliance status.
FAQ
What authentication mechanisms do agentic commerce payments use?
Agentic commerce payments use public-key cryptography for agent identity verification, where agents sign transactions with private keys that can be verified using public keys. Multi-signature authorization adds additional security for high-value transactions, requiring cryptographic signatures from multiple parties before execution. OAuth 2.0 scopes define what actions authenticated agents can perform.
How do compliance systems prevent unauthorized agent transactions?
Compliance systems implement real-time transaction monitoring using behavioral analysis and rule-based detection to identify suspicious patterns. Agents operate within granular permission scopes limiting transaction amounts, merchant categories, and time windows. Transactions deviating from these parameters are blocked before settlement. Suspicious Activity Reports are generated automatically for transactions meeting regulatory thresholds.
What happens if an agentic commerce payment is disputed?
Agentic commerce systems maintain immutable audit trails showing agent identity, authorization details, compliance checks performed, and settlement confirmation. These cryptographic proofs demonstrate that authorized agents executed transactions within their permission scope, providing strong evidence in chargeback disputes. The complete transaction record is available for regulatory review and dispute resolution.
How does the Universal Commerce Protocol standardize agentic payment security?
The UCP framework standardizes authentication requirements using public-key cryptography, defines granular authorization scoping models, mandates compliance logging requirements, and specifies tokenization standards for payment data. These standardizations ensure agents operating across different commerce networks maintain consistent security and compliance practices, reducing implementation burden and improving interoperability.
Leave a Reply