The Security Imperative in Agentic Commerce
Agentic commerce represents a fundamental shift in how transactions occur—autonomous software agents acting on behalf of buyers and merchants without real-time human intervention. Unlike traditional e-commerce where humans authorize each purchase, agentic systems make decisions, negotiate terms, and execute trades independently. This automation delivers efficiency gains, but introduces novel security vulnerabilities that traditional fraud prevention systems were never designed to address.
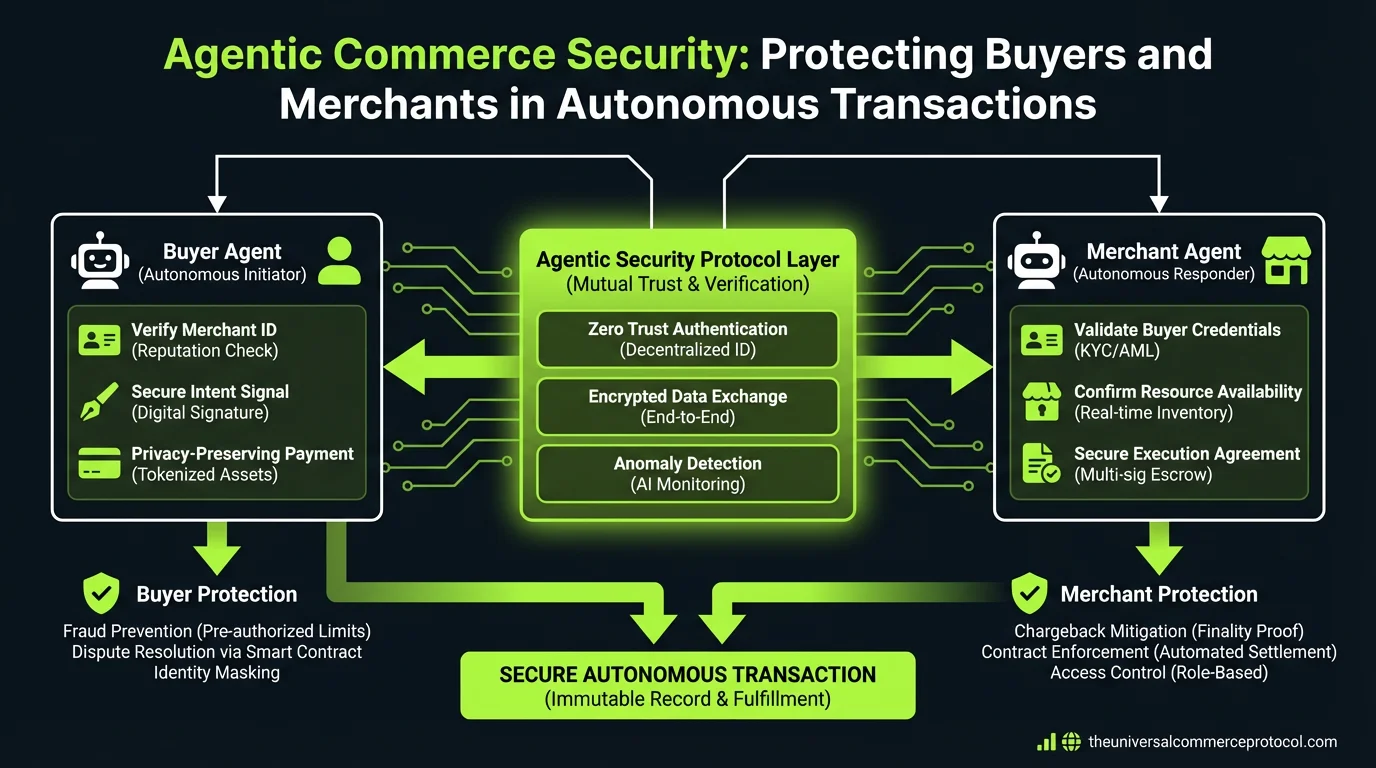
The Universal Commerce Protocol (UCP) recognizes that security in agentic commerce must address three interconnected challenges: authenticating the agent itself, verifying the principal’s identity and authorization, and establishing trust frameworks that operate across decentralized networks. Without robust security architecture, agentic commerce risks becoming a vector for sophisticated fraud, identity theft, and unauthorized financial transactions at scale.
Understanding Agentic Commerce Attack Surfaces
Agentic commerce systems present unique attack surfaces that differ fundamentally from traditional e-commerce fraud patterns. Because agents operate autonomously with pre-programmed parameters and access to financial instruments, compromising a single agent could enable fraudsters to execute thousands of unauthorized transactions before detection.
Agent Compromise and Credential Theft
When an agent’s credentials or private keys are compromised, attackers gain access to transaction authority without needing to impersonate the principal. A malicious actor could redirect purchases, modify payment instructions, or execute unauthorized trades. This differs from traditional account takeover, where the victim’s login credentials are stolen—in agentic systems, the agent itself becomes the attack target.
Principal Impersonation and Delegation Abuse
Fraudsters may attempt to register false principals or impersonate legitimate ones to deploy malicious agents. They could also exploit delegation mechanisms—where principals grant agents authority to act on their behalf—by creating agents with excessive permissions or extending their scope beyond intended parameters.
Man-in-the-Middle and Protocol Attacks
As agents communicate with merchants and other agents across networks, intercepted communications could enable attackers to modify transaction terms, redirect payments, or inject false information. Protocol-level vulnerabilities in how agents authenticate each other and validate transaction parameters create additional risk surfaces.
Collusion Between Agents and Bad Actors
Sophisticated fraud schemes could involve compromised merchant agents colluding with buyer agents to execute fraudulent transactions, generate false chargebacks, or manipulate transaction records. These coordinated attacks are difficult to detect using traditional fraud models designed for single-party fraud.
Identity Verification Frameworks for Agentic Systems
Establishing trust in agentic commerce requires robust identity verification that operates at multiple layers: verifying the principal (human or organization), the agent (software entity), and the relationships between them.
Principal Identity Verification
The foundation of agentic commerce security is confirming the identity of the principal who deploys the agent. This requires stronger verification than traditional Know Your Customer (KYC) processes, as agents will execute transactions autonomously with minimal human oversight.
- Multi-factor biometric verification: Principals should authenticate through multiple factors—facial recognition, fingerprint biometrics, or behavioral analysis—to deploy agents with transaction authority.
- Decentralized identity standards: Protocols like W3C Decentralized Identifiers (DIDs) enable portable identity verification across multiple commerce platforms without requiring centralized identity providers. Companies like Sovrin and Evernym have developed DID infrastructure that agentic commerce platforms can integrate.
- Blockchain-anchored identity: Storing identity verification records on immutable ledgers (such as Hyperledger Indy or Ethereum) creates auditable proof of identity verification that merchants can independently validate.
Agent Identity and Provenance Verification
Each agent must have verifiable identity, cryptographic credentials, and documented provenance—proof of where it originated and who deployed it. This enables merchants to make trust decisions about which agents to accept.
- Agent certificates and signing: Agents should be digitally signed by their creators or the platforms that deployed them, similar to code signing in software distribution. This proves the agent hasn’t been tampered with since deployment.
- Agent registries: Centralized or decentralized registries (similar to DNS for agents) can maintain records of registered agents, their creators, their permissions, and their transaction history. Ethereum Name Service (ENS) or similar systems could be extended to support agent identity.
- Behavior attestation: Third-party auditors can analyze agent code and behavior to issue attestations confirming the agent operates within stated parameters and doesn’t contain malicious logic.
Cryptographic Trust Mechanisms
Modern agentic commerce relies on cryptographic primitives to establish trust without requiring trusted intermediaries at every transaction layer.
Zero-Knowledge Proofs and Privacy-Preserving Verification
Zero-knowledge proofs (ZKPs) enable agents to prove facts about principals or transactions without revealing sensitive information. An agent could prove a principal has sufficient funds or valid credentials without exposing account balances or personal data. Companies like Polygon and StarkWare have developed ZK infrastructure that commerce platforms can leverage for privacy-preserving verification.
Threshold Cryptography and Multi-Signature Authorization
For high-value transactions, agents can require multiple signatures or approvals from different parties. Threshold schemes—where M-of-N parties must approve a transaction—prevent single points of failure. This is particularly important for merchant agents handling payments or for buyer agents executing large purchases.
Verifiable Credentials and Attestations
The W3C Verifiable Credentials (VC) specification provides a framework for cryptographically signed claims about identity, qualifications, or transaction history. Merchants could require buyer agents to present verifiable credentials proving the principal’s creditworthiness or transaction reputation before accepting their offers.
Fraud Detection in Autonomous Systems
Traditional fraud detection relies on human review and pattern matching against known fraud signatures. Agentic commerce requires real-time, algorithmic fraud detection that can identify suspicious agent behavior without human intervention.
Behavioral Analytics and Anomaly Detection
Machine learning models can establish baseline patterns for each agent’s transaction behavior—typical transaction sizes, frequency, merchant types, and geographic patterns. Deviations from these baselines trigger alerts or transaction holds. Platforms like Stripe and Fraud.net employ similar models for traditional e-commerce fraud detection and are beginning to adapt these for autonomous systems.
Graph Analysis and Relationship Mapping
Fraudsters often operate in coordinated networks. Graph databases can map relationships between principals, agents, merchants, and accounts to identify suspicious clusters. Detecting when multiple agents from different principals suddenly execute coordinated transactions with the same merchant is a signal of potential fraud.
Reputation Systems and Trust Scoring
Decentralized reputation systems track agent and principal behavior over time. Systems like Gitcoin Passport or Protocol Labs’ Filecoin reputation mechanisms assign trust scores based on transaction history, verification status, and dispute resolution outcomes. Merchants can use these scores to make accept/reject decisions.
Compliance and Regulatory Frameworks
Agentic commerce operates within existing regulatory regimes—payment regulations, consumer protection laws, anti-money laundering (AML) requirements—that were designed for human-mediated transactions. Compliance frameworks must adapt to autonomous execution while maintaining regulatory objectives.
Transaction Monitoring and AML Compliance
Financial regulators require transaction monitoring to detect money laundering, sanctions violations, and terrorist financing. Agentic commerce platforms must implement automated monitoring that flags suspicious patterns—rapid movement of funds through multiple accounts, transactions with sanctioned entities, or structuring to evade reporting thresholds—without requiring human review of every transaction.
Dispute Resolution and Chargeback Handling
When disputes arise between principals and merchants in agentic transactions, resolution must be automated yet fair. Smart contracts can implement dispute resolution logic—escrow mechanisms that hold funds pending dispute resolution, automated refund policies, or escalation to arbitration. Platforms like OpenZeppelin provide smart contract templates for escrow and dispute handling.
Audit Trails and Accountability
Regulatory compliance requires immutable records of who authorized what transaction, when, and why. Agentic commerce systems must maintain comprehensive audit trails—cryptographically signed records of agent deployments, authorization parameters, transaction execution, and any modifications to agent behavior. Blockchain-based systems like Hyperledger Fabric provide audit trail capabilities suitable for regulated commerce.
Building Trust in Decentralized Agentic Commerce
The Universal Commerce Protocol envisions agentic commerce operating across decentralized networks where no single entity controls all participants. In this environment, trust must be established algorithmically through cryptographic proofs and reputation systems rather than relying on a trusted central authority.
Standardized Security Requirements
The UCP defines minimum security standards that all agents and platforms must meet: cryptographic signing of transactions, identity verification of principals, agent code auditing, and participation in shared reputation systems. These standards create a baseline of trust across the ecosystem.
Interoperable Fraud Reporting
Participants in agentic commerce networks can share fraud intelligence—reports of compromised agents, fraudulent principals, or suspicious transaction patterns. Standardized formats enable this information to flow across platforms, improving collective fraud detection capabilities.
Insurance and Risk Transfer Mechanisms
As agentic commerce scales, insurance products will emerge to cover losses from agent compromise, fraud, or protocol failures. These mechanisms transfer risk from individual merchants and principals to insurers who can aggregate and manage risk across the ecosystem.
Implementation Best Practices
- Cryptographic key management: Agents require secure key storage and rotation. Hardware security modules (HSMs) or threshold key schemes prevent single points of failure.
- Continuous agent monitoring: Real-time monitoring of agent behavior, resource usage, and transaction patterns enables rapid detection of compromise or malfunction.
- Principal authorization limits: Agents should operate under explicit constraints—maximum transaction size, daily spending limits, approved merchant categories—that prevent runaway fraud.
- Regular security audits: Agent code should undergo periodic security audits by third parties to identify vulnerabilities before deployment.
- Incident response procedures: Clear procedures for responding to agent compromise, including immediate credential revocation, transaction reversal, and principal notification.
The Future of Agentic Commerce Security
As agentic commerce matures, security frameworks will incorporate emerging technologies—quantum-resistant cryptography to protect against future quantum computing threats, advanced AI for fraud detection, and decentralized governance systems for establishing security standards. The evolution of the Universal Commerce Protocol will continue adapting these mechanisms to protect participants while enabling the efficiency gains that make agentic commerce transformative.
FAQ
What is the difference between agentic commerce fraud and traditional e-commerce fraud?
Traditional e-commerce fraud typically involves compromising a human user’s account or credentials to make unauthorized purchases. Agentic commerce fraud involves compromising the agent itself or the authorization delegation, enabling an attacker to execute potentially thousands of autonomous transactions without the principal’s knowledge. The speed and scale of autonomous fraud is fundamentally different from traditional fraud patterns.
How can merchants verify that an agent is legitimate and authorized?
Merchants can verify agent legitimacy through cryptographic signatures proving the agent was deployed by a verified principal, checking the agent’s registration in trusted agent registries, reviewing the agent’s reputation score based on transaction history, and requiring the agent to present verifiable credentials from the principal. The Universal Commerce Protocol standardizes these verification mechanisms.
What role do smart contracts play in agentic commerce security?
Smart contracts implement security logic that executes automatically—escrow mechanisms that hold funds pending verification, transaction limits that prevent agents from exceeding authorized amounts, and dispute resolution procedures that activate when conflicts arise. Smart contracts create trustless security by removing the need for human oversight of every transaction.
How do regulations like KYC and AML apply to agentic commerce?
Agentic commerce platforms must still comply with KYC requirements by verifying the identity of principals who deploy agents, and AML requirements by monitoring transactions for suspicious patterns. The difference is that compliance is implemented algorithmically—automated identity verification at agent deployment time and real-time transaction monitoring—rather than through manual human review.
Leave a Reply