Agentic Commerce Payments: The Compliance and Security Imperative
Agentic commerce has transitioned from theoretical framework to operational reality in 2026. Autonomous agents—powered by large language models and reinforcement learning—now execute procurement, settlement, and payment workflows across supply chains, B2B marketplaces, and enterprise procurement platforms. Unlike traditional e-commerce where humans authorize each transaction, agentic commerce delegates payment authority to software agents operating within defined parameters and guardrails.
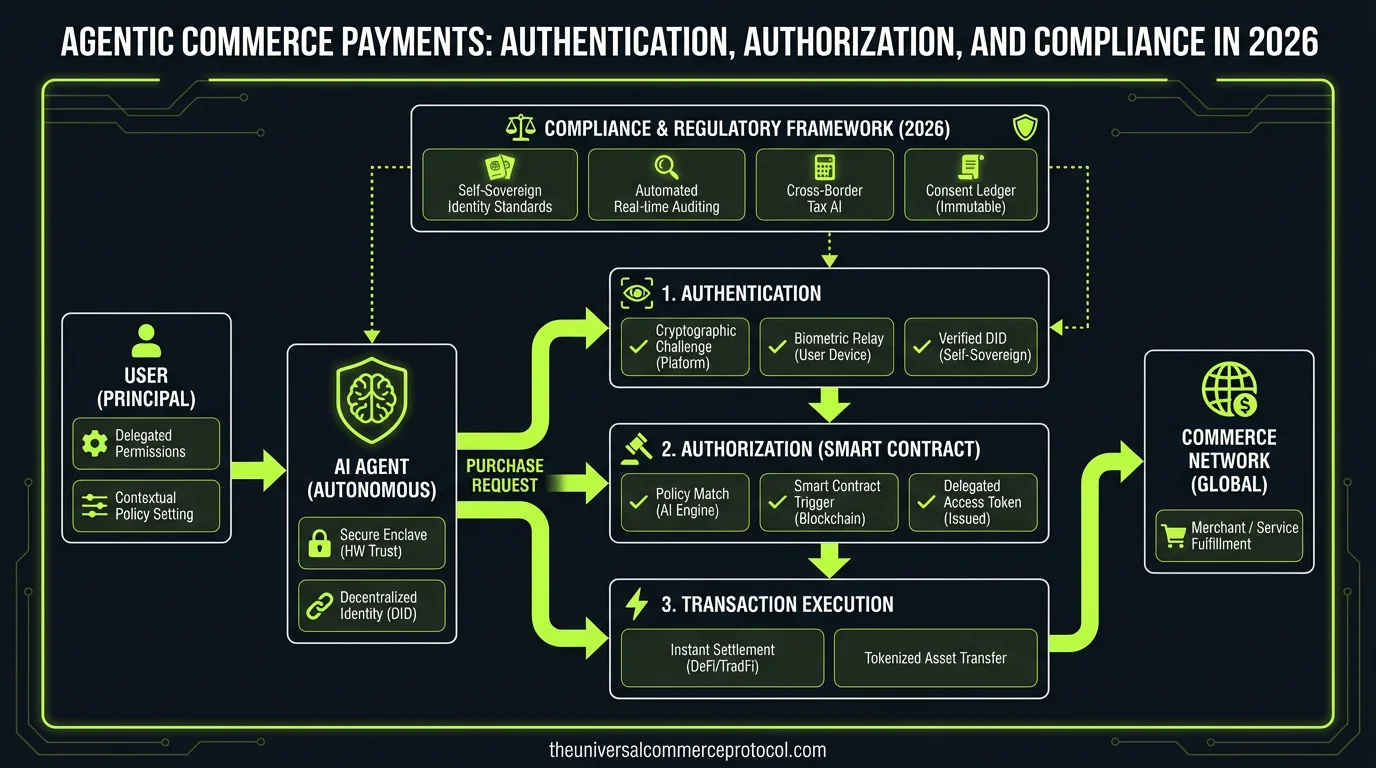
This shift introduces unprecedented compliance and security challenges. Payment flows that once required human review now occur at machine speed, across multiple jurisdictions, currencies, and regulatory regimes. The Universal Commerce Protocol (UCP) framework establishes the technical foundation for these transactions, but authentication, authorization, and compliance layers determine whether agentic payments remain trustworthy, auditable, and legally defensible.
Related articles: UCP Shipping Carrier Selection & Rate Optimization • UCP Security Best Practices for AI-Driven Commerce
Authentication in Autonomous Payment Flows
Agent Identity and Cryptographic Verification
In agentic commerce, “who” is making the payment decision is fundamentally ambiguous. Is it the agent? The enterprise that deployed the agent? The human stakeholder who set the agent’s parameters? Authentication frameworks must establish verifiable identity chains across all parties.
Leading implementations in 2026 use public key infrastructure (PKI) combined with decentralized identifiers (DIDs). Companies like Trinsic and Sovrin have deployed identity verification systems where agents hold cryptographic credentials issued by their parent organizations. These credentials are cryptographically signed and verifiable by payment processors, compliance auditors, and regulators without exposing the agent’s operational logic.
Enterprise adoption patterns show:
- Hardware Security Modules (HSMs): Organizations like JPMorgan Chase and Goldman Sachs operate payment agents that sign transactions using keys stored in FIPS 140-2 Level 3 HSMs, ensuring agent credentials cannot be compromised through software exploitation.
- Multi-signature authentication: Procurement agents at companies like Siemens and Schneider Electric require dual-key authorization—one from the agent’s cryptographic identity, one from the supervising enterprise’s compliance officer—before payments exceeding thresholds execute.
- Zero-Knowledge Proofs (ZKPs): Emerging implementations use ZKPs to authenticate agent actions without revealing the underlying decision logic, satisfying both security and intellectual property concerns. Protocols like Circom and zk-SNARK implementations enable agents to prove “I am authorized to make this payment” without disclosing the specific parameters driving that authorization.
Continuous Agent Attestation
Unlike static authentication, agentic commerce requires continuous verification that agents remain in compliant operational states. Trusted Execution Environments (TEEs) such as Intel SGX and ARM TrustZone now run payment agent logic, generating cryptographic attestations that prove the agent’s code hasn’t been modified and is executing within authorized parameters.
Payment networks including SWIFT, operated by the SWIFT organization, and emerging blockchain-based protocols like Ripple’s RippleNet now require TEE attestations before processing large-value agentic transactions. This prevents compromised agents from executing unauthorized payments even if their credentials are valid.
Authorization: Defining Agent Payment Authority
Capability-Based Authorization Models
Traditional authorization relies on role-based access control (RBAC): “Alice can approve payments up to $100,000.” Agentic commerce requires capability-based models that specify what agents can pay, to whom, under what conditions, and with what frequency.
The Object Capabilities (ocap) model, formalized by researchers at Agoric and implemented by companies like Stripe and Adyen in their agentic payment APIs, defines authorization as a set of cryptographic capabilities held by the agent:
- Vendor-specific capabilities: An agent can only transfer funds to pre-approved vendor accounts, cryptographically bound to specific bank routing numbers and tax IDs.
- Amount boundaries: Capabilities specify maximum transaction size, daily aggregate limits, and per-vendor spending caps. These are enforced at the protocol level, not just in application logic.
- Temporal constraints: Capabilities expire, require renewal, and can be revoked in real-time by human supervisors without redeploying agent code.
- Conditional execution: Capabilities trigger only when specific conditions are met—purchase orders are matched to invoices, inventory thresholds are breached, or price indices cross predetermined levels.
Attribute-Based Authorization (ABAC) for Compliance
Regulatory requirements vary by transaction context: payments to high-risk jurisdictions require enhanced due diligence; payments to politically exposed persons (PEPs) trigger additional verification; payments in certain sectors require licensing confirmation.
Attribute-based authorization systems now evaluate transaction attributes against compliance policies in real-time. Companies like Sift Science and Feedzai operate authorization layers that:
- Cross-reference payee entities against OFAC, EU sanctions lists, and local regulatory databases.
- Evaluate transaction risk scores incorporating geolocation, historical patterns, and market conditions.
- Invoke human review workflows when risk scores exceed thresholds, pausing agent execution until compliance officers approve.
- Generate audit logs documenting the authorization decision rationale for regulatory inspection.
Major financial institutions operating agentic payment systems—including BNY Mellon, State Street, and Deutsche Bank—implement ABAC layers that integrate with their compliance management platforms, ensuring agents cannot circumvent regulatory controls regardless of their capability grants.
Regulatory Compliance and Audit Requirements
Jurisdictional Payment Regulation in 2026
Agentic commerce operates across regulatory jurisdictions with divergent requirements. The EU’s Payment Services Directive 2 (PSD2) mandates strong customer authentication (SCA) for all electronic payments; the US Treasury FinCEN guidance requires beneficial ownership verification for cross-border transactions; Singapore’s Monetary Authority (MAS) requires explainability for algorithmic trading and settlement decisions.
Compliance frameworks must encode these requirements into payment authorization logic:
- EU/UK compliance: Payment agents operating in European jurisdictions implement SCA through Open Banking APIs (PSD2 XS2A standard), where agent-initiated payments trigger customer authentication via banking apps or biometric verification.
- US AML/CFT: Treasury regulations require agents to conduct Know Your Customer (KYC) and Customer Due Diligence (CDD) before payments to new counterparties. Agents integrate with compliance data providers like LexisNexis and Refinitiv to verify counterparty risk profiles.
- Asia-Pacific requirements: MAS, Hong Kong’s SFC, and Australia’s ASIC now require agentic payment systems to maintain explainability—agents must document why they authorized specific transactions, enabling regulators to audit decision logic.
Continuous Audit and Regulatory Reporting
In 2026, regulatory reporting has become continuous rather than periodic. Payment agents generate real-time compliance data feeds that flow to regulatory sandboxes and compliance platforms operated by central banks and financial regulators.
The Bank for International Settlements (BIS) and the Financial Stability Board (FSB) have established standardized reporting schemas for agentic transactions, adopted by major payment networks including Visa, Mastercard, and American Express. These schemas capture:
- Agent identity and deployment organization.
- Transaction authorization rationale and decision attributes.
- Counterparty risk assessments and sanctions screening results.
- Exception handling and human override instances.
- Compliance policy versions enforced at transaction time.
Institutions like JPMorgan Chase now operate compliance data lakes that ingest agentic payment transaction records in real-time, enabling regulators to query payment flows and audit agent behavior without manual reporting burden.
Immutable Transaction Records and Blockchain Integration
Regulatory requirements for transaction immutability have driven adoption of distributed ledger technology (DLT) for agentic payment settlement. Companies including Citi, BNY Mellon, and Accenture operate private blockchain networks (using Hyperledger Fabric, Corda, or proprietary DLTs) where agentic payment transactions are recorded in cryptographically sealed ledgers that cannot be retroactively modified.
These systems enable regulators to audit complete transaction histories with cryptographic proof that records haven’t been tampered with. The immutable record includes authentication evidence, authorization decisions, and compliance determinations—creating an auditable chain of custody for every agent-initiated payment.
Emerging Threats and Defense Mechanisms
Agent Prompt Injection and Authorization Bypass
As agents rely on natural language processing and large language models, adversaries now attempt to manipulate agent behavior through prompt injection—embedding malicious instructions in transaction data that cause agents to override authorization constraints.
Defense mechanisms in 2026 include:
- Semantic firewalls: Payment authorization layers parse transaction requests for semantic anomalies and injection patterns, quarantining suspicious requests for human review.
- Capability isolation: Agents operate in sandboxed environments where they cannot directly access payment authorization systems; they can only invoke pre-defined, cryptographically sealed authorization functions.
- Adversarial testing: Organizations conduct regular red-team exercises where security teams attempt to manipulate agents into unauthorized payments, validating defense effectiveness.
Supply Chain Payment Fraud
Agentic commerce has created new fraud vectors where attackers compromise supplier accounts, redirect payments to fraudulent bank accounts, or inject false invoices into procurement workflows. Defense mechanisms include:
- Payee verification: Agents verify that payment destinations match pre-registered vendor accounts using cryptographic proofs and real-time bank verification APIs.
- Invoice matching: Agents cross-reference payment requests against purchase orders, receipts, and inventory records before executing payments, preventing payments for non-existent goods.
- Behavioral anomaly detection: Machine learning systems monitor agent payment patterns for anomalies (unusual vendors, geographic shifts, timing changes) and escalate suspicious transactions to compliance teams.
FAQ: Agentic Commerce Payment Compliance
1. How do regulators audit agentic payment decisions if the underlying AI logic is proprietary?
Regulators don’t need to audit the AI model itself—they audit the transaction outcomes and decision documentation. Agentic payment systems must maintain detailed logs showing what attributes were evaluated, what policies were applied, and why the authorization decision was made. This explainability layer is separate from the proprietary model. Regulators can verify that the system followed its documented compliance policies without accessing the underlying neural network weights. If an agent makes a questionable payment decision, regulators can request the decision rationale and audit trail.
2. What happens if an agent makes an unauthorized payment due to a security vulnerability?
Liability frameworks are still evolving, but the consensus in 2026 is that the deploying organization (the enterprise that deployed the agent) bears primary liability, not the AI vendor. This creates incentives for enterprises to implement robust security controls. Payment networks and regulators are establishing “safe harbor” provisions: if an organization can demonstrate it implemented industry-standard authentication, authorization, and monitoring controls, liability may be limited. However, if an organization deployed an agent without proper security guardrails, regulators and payment networks hold them fully accountable.
3. Can agentic payment systems operate across multiple jurisdictions with different compliance requirements?
Yes, but only with multi-layered compliance logic. Payment agents now operate with jurisdiction-aware policy engines that evaluate transactions against the specific regulatory regime of the payer, payee, and transaction settlement location. An agent might apply EU PSD2 rules for European transactions, US AML/CFT rules for US transactions, and Singapore MAS rules for APAC transactions—all within a single agent instance. This requires sophisticated policy management systems and continuous regulatory monitoring to ensure policies remain current as regulations evolve.
4. How do enterprises balance agent autonomy with compliance risk?
The industry has converged on a tiered autonomy model: agents operate with full autonomy for low-risk, routine transactions (routine vendor payments within normal parameters); they escalate medium-risk transactions to human review queues; they halt high-risk transactions and request explicit approval. This preserves the efficiency benefits of agentic commerce while maintaining human oversight for compliance-sensitive decisions. Risk scoring is continuous, so as market conditions change or new sanctions designations emerge, the same transaction type might move from autonomous to human-review tier.
Frequently Asked Questions
What is the Universal Commerce Protocol (UCP)?
The Universal Commerce Protocol (UCP) is an open standard developed to enable AI agents to autonomously conduct commerce transactions across any platform.
How does UCP enable agentic commerce?
UCP provides standardized APIs and protocols so AI agents can discover products, negotiate terms, and complete purchases without human intervention, working across any compatible commerce platform.
Why should businesses implement UCP?
UCP adoption reduces integration costs, opens revenue channels to AI-driven buyers, and future-proofs commerce infrastructure as agentic purchasing becomes mainstream.
Leave a Reply