Introduction to Agentic Trust Frameworks
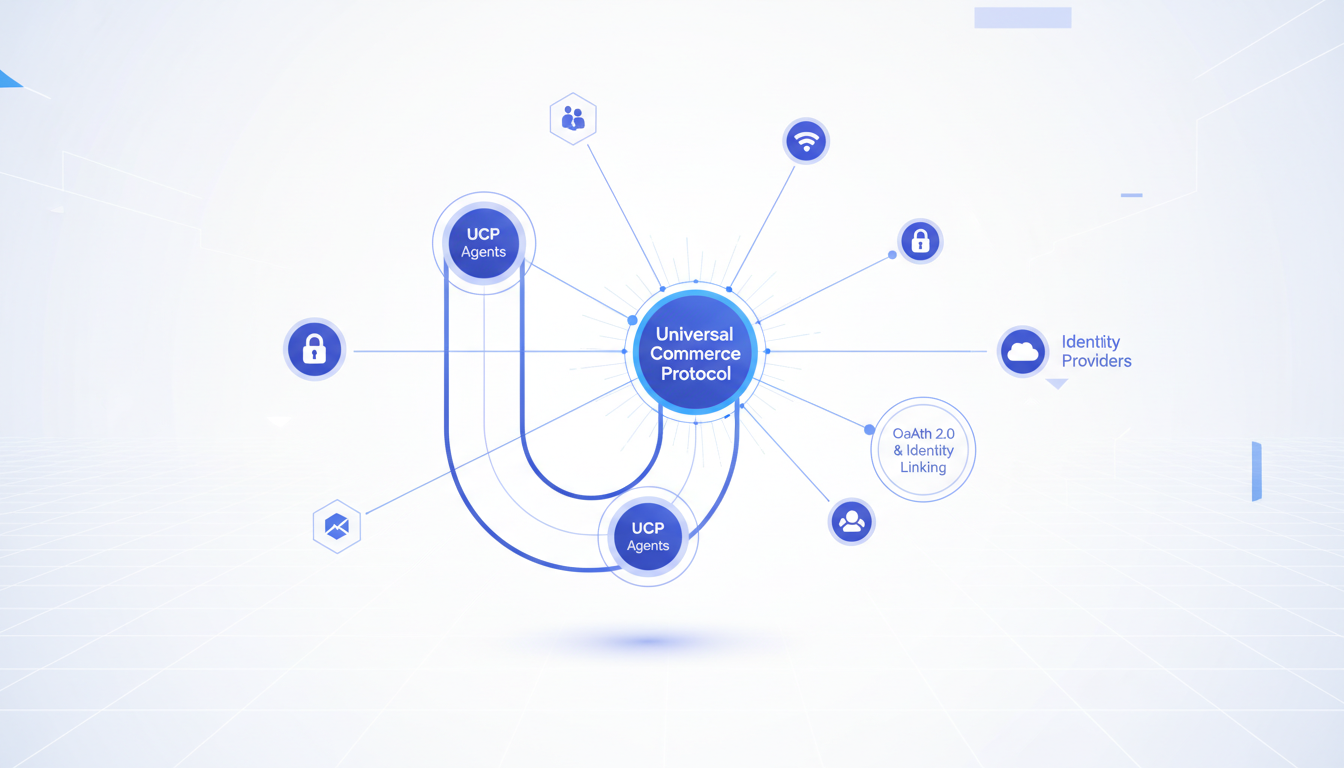
In the evolving landscape of Agentic Commerce, the traditional model of session-based authentication is being replaced by persistent, delegated authority. As part of the Universal Commerce Protocol (UCP), the concept of UCP Identity Linking ensures that an AI agent—whether running on Gemini, via the Model Context Protocol (MCP), or within a merchant’s custom environment—can act with the explicit permission of a human user. This technical guide explores the implementation of OAuth 2.0 flows and identity linking strategies designed to secure these autonomous transactions.
The Identity Linking Workflow
Identity linking in UCP is a multi-step handshake that binds a Google Identity to a Merchant’s internal customer record. This process is essential for ensuring that when an agent initiates a request, the merchant can verify the user’s eligibility, pricing tiers, and loyalty status. The workflow follows a strict Zero-Trust architecture.
The Three-Way Trust Model
The UCP identity model involves three distinct parties: the User (the identity owner), the Agent (the delegated entity, often powered by Gemini), and the Merchant (the service provider). Unlike traditional web apps where the user is the primary actor, the agent acts as a middleman that requires programmatic access. The connection is established via the OAuth 2.0 Authorization Code Flow with Proof Key for Code Exchange (PKCE) to prevent interception during the agentic handoff.
Step-by-Step Handshake
- Initial Trigger: The user interacts with a Gemini-powered agent. The agent identifies the need to perform a transaction through a UCP-compliant merchant.
- Discovery: The agent queries the merchant’s
/.well-known/ucp-configurationendpoint to locate the authorization server. - Redirection & Authentication: The user is prompted to link their Google account. This uses the Google Identity Services (GIS) to provide a seamless login.
- Authorization Code Exchange: Once authenticated, the merchant issues an authorization code which is exchanged by the UCP gateway for an access token and a refresh token.
- Mapping: The merchant’s backend maps the
sub(subject) claim from the Google ID token to the merchant’s internal UUID.
Configuring OAuth 2.0 Scopes for UCP
Granular control over permissions is vital for agentic security. When an agent requests access to a user’s commerce data, it should only hold the minimum necessary scopes to complete the task. Within the UCP framework, we differentiate between discovery scopes and transactional scopes.
| Scope Type | Google API Scope | UCP Functional Purpose |
|---|---|---|
| Identity | openid profile email |
Basic user identification and linking. |
| Payments | https://www.googleapis.com/auth/payments.make_payment |
Permits the agent to trigger Google Pay transactions. |
| Merchant Feed | https://www.googleapis.com/auth/content |
Allows the agent to verify real-time stock and regional pricing. |
| UCP Specific | https://ucp.api/v1/orders.create |
Custom scope for agentic order placement. |
Native vs. Embedded Checkout Paths
The implementation of identity linking varies significantly based on the checkout path. In a Native Checkout scenario, the agent facilitates the entire transaction within the Google ecosystem (e.g., inside the Gemini interface). Here, identity linking is deep; the agent holds the token and passes it to the Merchant via a JSON-RPC call. In an Embedded Checkout path, the agent directs the user to a merchant-hosted micro-frontend. In this case, the identity link is passed as a secure state parameter to ensure the session remains consistent across the handoff.
The Role of MCP in Identity Propagation
The Model Context Protocol (MCP) serves as the transport layer for context between the LLM and the external tools. When implementing identity linking, the MCP server must act as a secure vault for OAuth tokens. Developers should implement a ‘Token-Aware Toolset’ where every tool call made by the LLM is automatically enriched with the Bearer token of the linked user. This prevents the LLM from ever seeing the raw credentials, maintaining a clean separation of concerns.
Token Revocation and Agent Lifecycle Management
The lifecycle of an agent’s authority must be strictly managed to prevent unauthorized long-term access. Unlike human sessions that might last for weeks, agentic tokens often have shorter TTLs (Time-To-Live) but rely on refresh tokens for background tasks like order tracking.
Security and Revocation Triggers
UCP-compliant merchants must implement a robust revocation strategy. If a user unlinks their Google account from the merchant’s settings, a backchannel_logout notification should be sent to the UCP gateway. This immediately invalidates all active access tokens held by the agent. Furthermore, the UCP protocol supports Risk Signals. If Google’s security systems detect suspicious activity on the user’s account, a signal is broadcasted to the merchant to pause all agentic commerce activities associated with that identity.
Handling Token Expiration in Gemini
When Gemini attempts a tool call and receives a 401 Unauthorized response, the MCP implementation must be capable of a silent refresh. If the refresh token is also expired, the agent must gracefully handle the failure by asking the user to re-authenticate: “I need you to re-verify your merchant account to complete this purchase.” This ensures the user remains in the loop for high-stakes security events.
Conclusion: The Future of Verified Agentic Commerce
By implementing a rigorous OAuth 2.0 and identity linking strategy, developers enable a world where AI agents can be trusted with financial autonomy. Leveraging the Universal Commerce Protocol alongside Google’s identity infrastructure creates a framework where every ‘Buy’ command is backed by a verified, authorized, and revocable link. As we move toward more complex agentic behaviors, these security fundamentals will remain the cornerstone of user trust in the Google AI ecosystem.
Frequently Asked Questions
What is the Universal Commerce Protocol (UCP)?
The Universal Commerce Protocol (UCP) is an open standard developed to enable AI agents to autonomously conduct commerce transactions across any platform.
How does UCP enable agentic commerce?
UCP provides standardized APIs and protocols so AI agents can discover products, negotiate terms, and complete purchases without human intervention, working across any compatible commerce platform.
Why should businesses implement UCP?
UCP adoption reduces integration costs, opens revenue channels to AI-driven buyers, and future-proofs commerce infrastructure as agentic purchasing becomes mainstream.
Leave a Reply